May 09, 2023 – Calgary, AB, Canada – Wedge Networks Inc. (“Wedge”), a market leader in Real-Time Threat Prevention solutions, today announced that Edgecore Networks, a leading provider of traditional and open network solutions for enterprises, data centers, and telecommunication service providers, has partnered with Wedge Networks to offer a next-generation network security solution to its customers. Wedge Networks’ Wedge Cloud Network Defense (WedgeCND™), is a cloud-managed security service designed to provide comprehensive security protection.
Through this partnership, WedgeCND™ is now available as an add-on for Edgecore’s Wi-Fi 6 series access points through its ecCLOUD cloud controller. This partnership offers Edgecore’s customers access to a range of optimized Security-as-a-Service (SECaaS) features seamlessly integrated into their networks, providing ubiquitous Wi-Fi network security protection.
WedgeCND™ is an innovative cloud-managed security service designed to protect cloud-managed computing devices. With the activation of WedgeCND™’s security add-on on the ecCLOUD, all hosts and endpoints accessing the Internet through Edgecore Wi-Fi 6 access points registered to ecCLOUD will be automatically protected against all types of threats, including malware, ransomware, phishing, and malicious websites. Leveraging robust cloud computing capacity and working at the network layer, WedgeCND™ provides the most advanced professional network security detection and protection, without the need for dedicated network security software and hardware.
“With the growing use of intelligent endpoints, customers require a simple, fast, and effective network security solution. This integration provides a seamless and comprehensive security solution for Edgecore’s customers, making network security protection simple and affordable for everyone.”
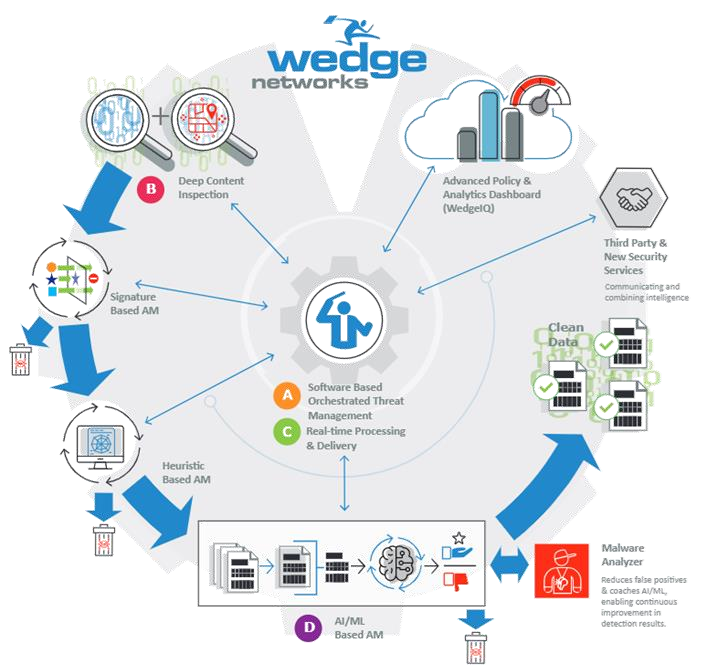
WedgeCND™’s patented technologies in high-performance cloud network security and high-accuracy threat detection with machine learning and inferencing algorithms provide true real-time performance that is not bound by hardware-based limitations, enabling industry-leading real-time threat prevention abilities. Additionally, the service’s automated and continuously learning AI-based Neural Engine can recognize never-before-seen malware in real time, providing customers with unparalleled protection against new and emerging threats.
Key Features:
- Plug-and-play activation for easy installation without the need for dedicated network security software and hardware
- Professional-grade network security protection combining multiple cloud-based detection engines including AI machine learning, behavior analysis, big data-based anomaly detection, and real-time security intelligence
- Real-time threat and intrusion blocking that filters and blocks threats in the data flow, preventing attacks on connected hosts and endpoints
- Regular security event reports are sent to customer email to provide a clear overview of all discovered and blocked threats
- Subscription-based annually with the option for customers to activate or cancel the service at any time, making it an affordable and flexible option for all wireless AP users, including chain restaurants/cafes, hotels, shopping malls, airports, and SOHOs.
“ecCLOUD is one of the largest managed Wi-Fi network platforms in the world. The activation of WedgeCND™ represents an important milestone in Wedge’s collaboration with Edgecore, providing large-scale, cost-effective cyber security solutions for ecCLOUD customers,” said Dr. Hongwen Zhang, CEO & CTO (Co-founder) of Wedge. Furthermore, “As a leader in the global open networking ecosystem, Edgecore plays a crucial role in facilitating current and future digital transformation use cases. We are honored to work alongside Edgecore to safeguard the security and integrity of these critical applications.”
The collaboration between Edgecore Networks and Wedge Networks enables customers to seamlessly integrate WedgeCND™ into their networks and enjoy comprehensive security features and benefits, making ecCLOUD the cloud controller solution of choice.
This press release can be found on the Edgecore website at https://www.edge-core.com/news-inquiry.php?cls=1&id=993 or for more information on the solution at WedgeCND – ecCLOUD Add-On | Edgecore (edge-core.com)
About Edgecore Networks
Edgecore Networks Corporation is a wholly-owned subsidiary of Accton Technology Corporation, the leading network ODM. Edgecore Networks delivers wired and wireless networking products and solutions through channel partners and system integrators worldwide for data centers, service providers, enterprises, and SMB customers. Edgecore Networks is the leader in open networking, providing a full line of open Wi-Fi access points, packet transponders, virtual PON OLTs, cell site gateways, aggregation routers, and 1G, 10G, 25G, 40G, 100G, and 400G OCP AcceptedTM switches that offer a choice of commercial and open-source NOS and SDN software.
For more information, visit wifi.edge-core.com or contact sales@edge-core.com.
About Wedge Networks
Wedge Networks Inc. is an innovator and developer of cybersecurity technologies utilizing advanced AI techniques providing intelligent Real-Time Threat Prevention solutions for the machine economy. Our innovation is a patented software platform, specifically designed for an increasingly connected world, that enables real-time security services rollout across the network from the edge to the cloud in strategic partnership with MSPs and OEMs. Wedge is headquartered in Calgary, Canada with international teams in the North America, Asia Pacific, Europe, and the Middle East and North Africa regions. Today, Wedge’s products prevent advanced security threats for many millions of endpoints in enterprises, governments, and critical infrastructures globally.
For more information, visit www.wedgenetworks.com
Cautionary Statements and Forward-Looking Information
This
release contains forward-looking statements, which are based on current
expectations, estimates, and projections about the Corporation’s
business and prospects, as well as management’s beliefs, and certain
assumptions made by management. Words such as “anticipates,” “expects,”
“intends,” “plans,” “believes,” “seeks,” “estimates,” “may,” “should,”
“will” and variations of these words are intended to identify
forward-looking statements. Such statements speak only as of the date
hereof and are subject to change. The forward-looking statements
contained in this news release are made as of the date hereof and Wedge
undertakes no obligation to update, publicly or otherwise, or revise any
forward-looking information, whether as a result of new information,
future events or otherwise unless expressly required by applicable
securities laws. The forward-looking information contained in this press
release are expressly qualified by this cautionary statement. Readers
are cautioned that any such forward-looking statements are not
guarantees of future business activities and involve risks and
uncertainties, and that the Corporation’s future business activities may
differ materially from those in the forward-looking statements as a
result of various factors , including, but not limited to: expansion and
business strategies, anticipated growth opportunities, the impact of
the COVID-19 pandemic, general economic, market or business conditions,
the amount of fundraising necessary to perform on its business
objectives, operational risks, the ability of the Corporation to raise
necessary funds for its business objectives, and the outcome of
commercial negotiations. Such statements are not guarantees of future
performance and are subject to certain risks, uncertainties, and
assumptions that are difficult to predict. Accordingly, actual results
could differ materially and adversely from those expressed in any
forward-looking statements as a result of various factors. There can be
no assurances that such information will prove accurate and, therefore,
readers are advised to rely on their own evaluation of such
uncertainties. Although the Company believes that the assumptions and
factors on which such forward-looking statements is based are
reasonable, undue reliance should not be placed on the forward-looking
statements as the Company can give no assurance that it will prove to be
correct or that any of the events anticipated by such forward-looking
statements will transpire or occur, or if any of them do so, what
benefits the Company will derive therefrom.