Snake is in the news as of late. No, not the one of the 2019 Chinese Zodiac but of the malware variation. Detected as “Trojan.Win32.Antavmu.asdd”, Snake works like most ransomware. It doesn’t touch your operating system files and programs so your computer still starts up and provides you with a working system. And, like most other ransomware, any other important files such as documents, photos, videos, spreadsheets, etc, are all scrambled and locked up with a randomly chosen encryption key.
Here’s the thing. With Snake, the scrambled files will consist of the encrypted content overwriting the original data with decryption info added on at the end. The original filenames and directories are are recorded, with the decryption key stored as well, with a special tag “EKANS” (“SNAKE” – backwards), finishing off the encrypted file.
Similarly to other ransomware, Snake uses a hybrid encryptions system with symmetric cryptography used to lock up the files but then public-key encryption used to lock up the decryption key. The reason being that symmetric cryptography is ideally suited for scrambling large amounts of data while public-key cryptography is better suited for small amounts but allows for two keys, instead of one, where the key used to lock up the data can’t be used to unlock it.
However, Snake is a bit different from other ransomware. While most ransomware denote scrambled files by adding unusual extensions to filenames so that they stand out, the Snake malware adds a different, randomly chosen string of characters, onto the names of encrypted files; making it more difficult to determine which files have been affected through name alone.
From there, the malware drops a “What happened to your files?” document onto your desktop, or in this case, it writes a file called “Fix-Your-Files.txt” into the Windows public desktop, where it shows up in the background for every user on the affected system. Unfortunately, the way the malware is written, with the expectation of having administrator access across the compromised network, the bad actors that are perpetrating this crime don’t intend on targeting individual users on the network but are looking to take their time and attack everyone, for a much more egregious outcome.
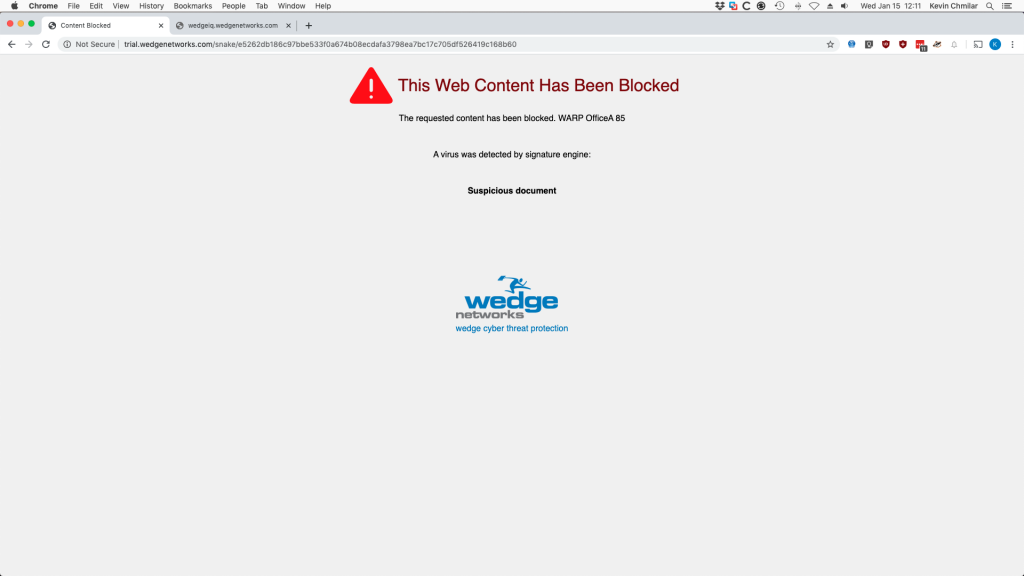
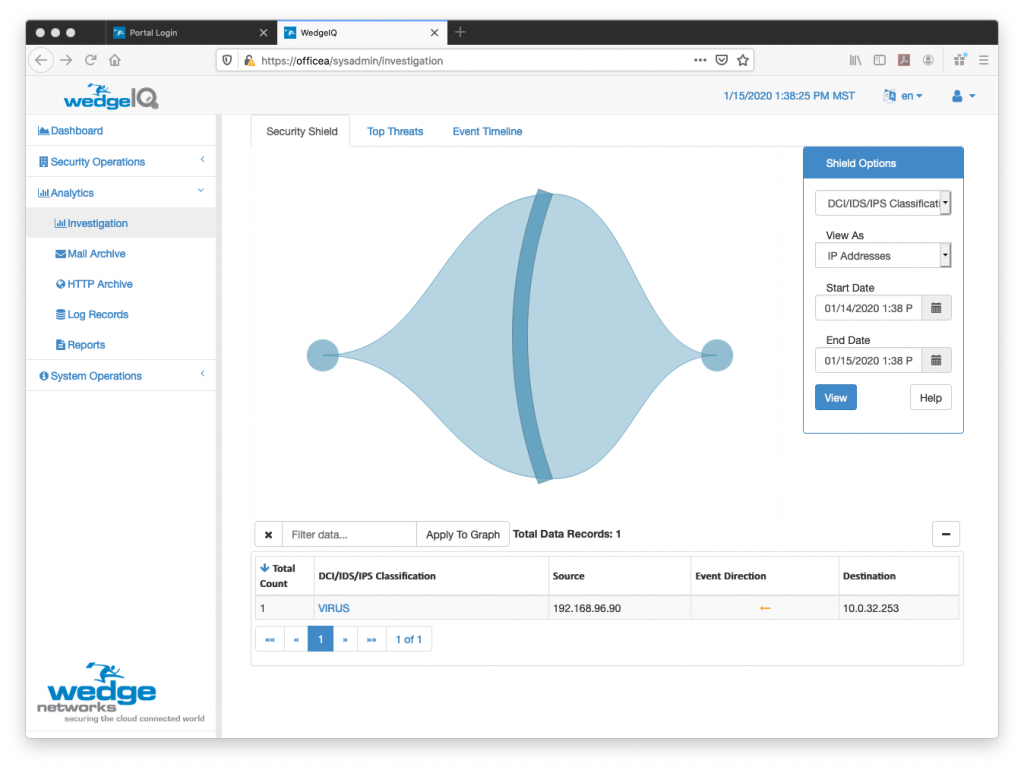
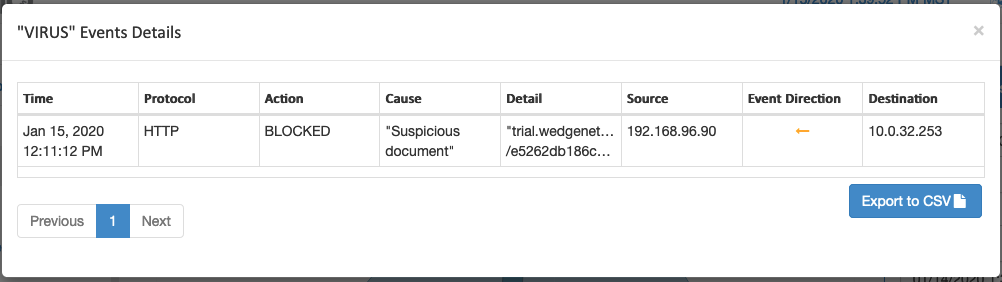
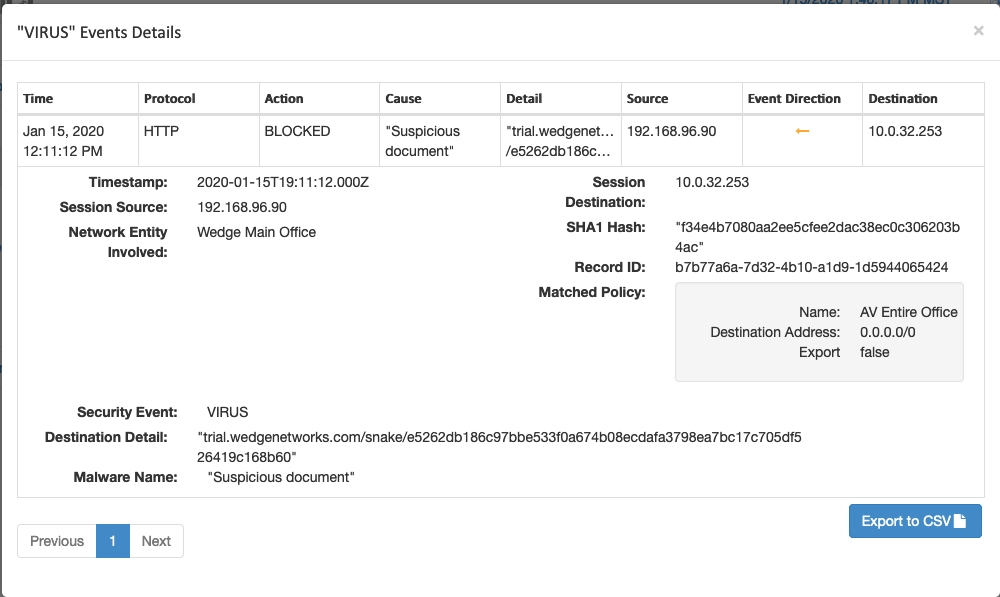
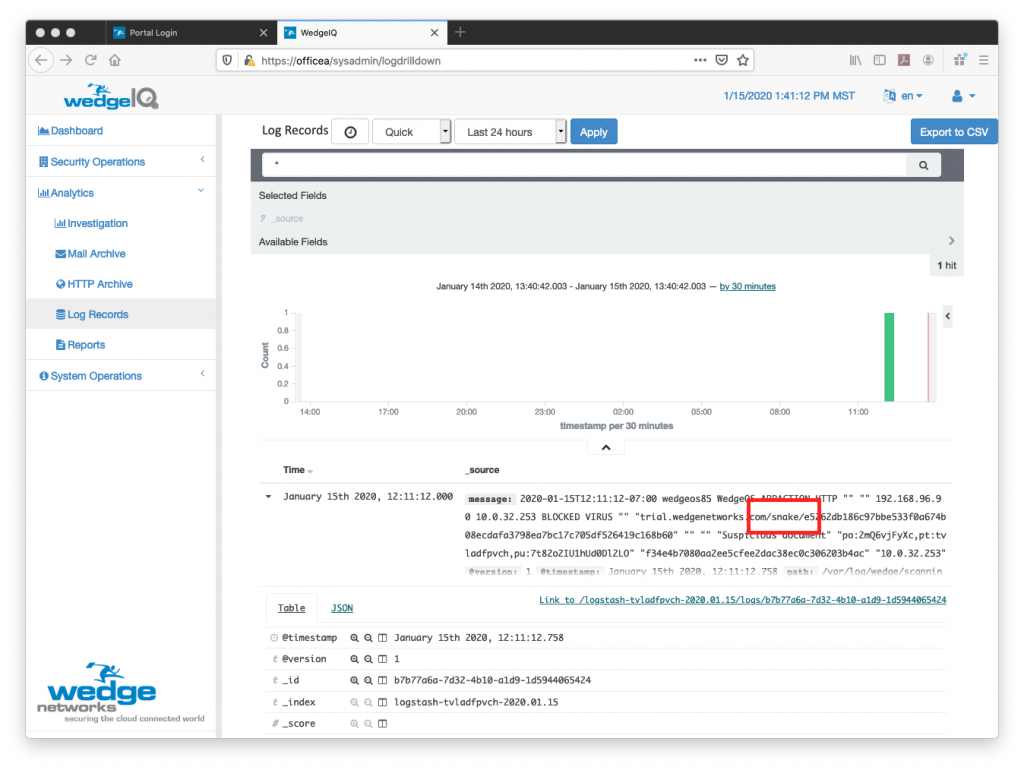
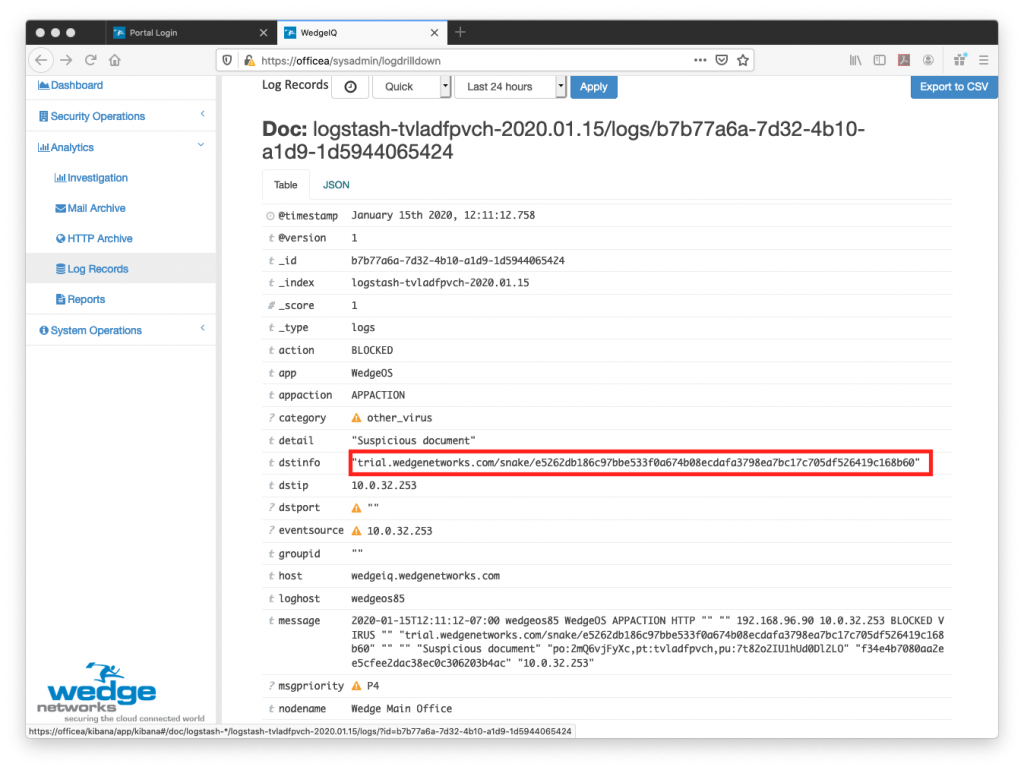
But there is a positive outcome to this story! As it turns out, the Snake ransomware is still ransomware at its core and because of the various key elements of the code, it can still be detected and blocked. Although many solutions out there are unable to detect it because they are still just looking at the packets and not the content itself, WedgeAMB, with Deep Content Inspection in its underlying platform, is able to do just that. By looking at the whole content, combined with AI and machine-learning abilities that can detect the “INTENT” of the content; despite variations in the malware itself, WedgeAMB can detect and BLOCK the malware in real-time. The malware is unable to even enter the network; preventing any and all damage from occurring. This can be evidenced in the screen-shots from WedgeIQ below, showing that the Snake malware was stopped in its tracks.

Now, hopefully your organization was not affected by this dastardly piece of ransomware as it has many other organizations out there. If you are concerned that perhaps your security systems might not be able to detect and block this and other ransomware variations, give us a shout! Wedge provides a FREE 90 Day trial of our Wedge Advanced Malware Blocker, which uses Deep Content Inspection along with Orchestrated Threat Management that incorporates best-of-breed security solutions and AI to detect and block ALL malware in real-time. Contact us at: info@wedgenetworks.com. Let’s usher out the Chinese Year of the Snake and protect ourselves from the Snake malware while ushering in a much better 2020 Year of the Rat!


